
Filter News
Area of Research
News Type
News Topics
- (-) 3-D Printing/Advanced Manufacturing (11)
- (-) Cybersecurity (7)
- (-) Nuclear Energy (9)
- Advanced Reactors (3)
- Artificial Intelligence (4)
- Big Data (2)
- Bioenergy (9)
- Biology (2)
- Biomedical (3)
- Clean Water (2)
- Composites (3)
- Computer Science (20)
- Energy Storage (1)
- Environment (11)
- Exascale Computing (1)
- Frontier (2)
- Fusion (4)
- Grid (2)
- Isotopes (3)
- Machine Learning (1)
- Materials Science (15)
- Mercury (2)
- Microscopy (5)
- Nanotechnology (8)
- Neutron Science (13)
- Physics (11)
- Polymers (2)
- Quantum Science (8)
- Security (7)
- Summit (5)
- Sustainable Energy (5)
- Transportation (6)
Media Contacts

The next cohort of Innovation Crossroads fellows at Oak Ridge National Laboratory will receive support from the U.S. Department of Energy’s Advanced Manufacturing Office (AMO) and the Tennessee Valley Authority (TVA). Officials made the announcement today at th...
Qrypt, Inc., has exclusively licensed a novel cyber security technology from the Department of Energy’s Oak Ridge National Laboratory, promising a stronger defense against cyberattacks including those posed by quantum computing.
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.
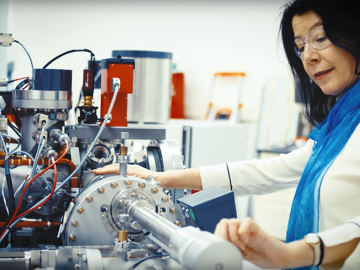
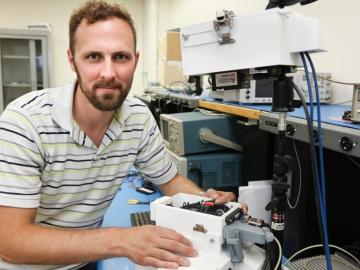
It may take a village to raise a child, according to the old proverb, but it takes an entire team of highly trained scientists and engineers to install and operate a state-of-the-art, exceptionally complex ion microprobe. Just ask Julie Smith, a nuclear security scientist at the Depa...

While serving in Kandahar, Afghanistan, U.S. Navy construction mechanic Matthew Sallas may not have imagined where his experience would take him next. But researchers at Oak Ridge National Laboratory certainly had the future in mind as they were creating programs to train men and wome...

Virginia-based Lenvio Inc. has exclusively licensed a cyber security technology from the Department of Energy’s Oak Ridge National Laboratory that can quickly detect malicious behavior in software not previously identified as a threat.


