
Artificial intelligence tools secure tomorrow’s electric grid
Sometimes solutions to the biggest problems can be found in the smallest details. The work of biochemist Alex Johs at Oak Ridge National Laboratory bears this out, as he focuses on understanding protein structures and molecular interactions to resolve complex global problems like the spread of mercury pollution in waterways and the food supply.
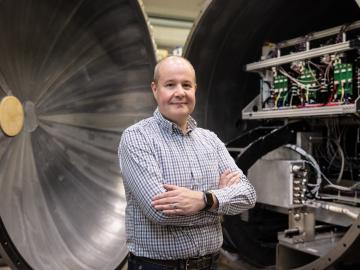
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.

