
Katy Bradford: Cassette approach offers compelling construction solution
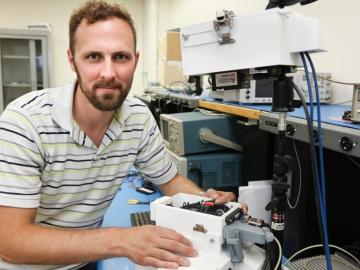
As leader of the RF, Communications, and Cyber-Physical Security Group at Oak Ridge National Laboratory, Kerekes heads an accelerated lab-directed research program to build virtual models of critical infrastructure systems like the power grid that can be used to develop ways to detect and repel cyber-intrusion and to make the network resilient when disruption occurs.

